A computer virus[1] is a type of computer program that, when executed, replicates itself by modifying other computer programs and inserting its own code into those programs.[2][3] If this replication succeeds, the affected areas are then said to be «infected» with a computer virus, a metaphor derived from biological viruses.[4]
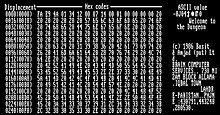
Hex dump of the Brain virus, generally regarded as the first computer virus for the IBM Personal Computer (IBM PC) and compatibles
Computer viruses generally require a host program.[5] The virus writes its own code into the host program. When the program runs, the written virus program is executed first, causing infection and damage. By contrast, a computer worm does not need a host program, as it is an independent program or code chunk. Therefore, it is not restricted by the host program, but can run independently and actively carry out attacks.[6][7]
Virus writers use social engineering deceptions and exploit detailed knowledge of security vulnerabilities to initially infect systems and to spread the virus. Viruses use complex anti-detection/stealth strategies to evade antivirus software.[8] Motives for creating viruses can include seeking profit (e.g., with ransomware), desire to send a political message, personal amusement, to demonstrate that a vulnerability exists in software, for sabotage and denial of service, or simply because they wish to explore cybersecurity issues, artificial life and evolutionary algorithms.[9]
Computer viruses cause billions of dollars’ worth of economic damage each year.[10] In response, an industry of antivirus software has cropped up, selling or freely distributing virus protection to users of various operating systems.[11]
HistoryEdit
The first academic work on the theory of self-replicating computer programs was done in 1949 by John von Neumann who gave lectures at the University of Illinois about the «Theory and Organization of Complicated Automata». The work of von Neumann was later published as the «Theory of self-reproducing automata». In his essay von Neumann described how a computer program could be designed to reproduce itself.[12] Von Neumann’s design for a self-reproducing computer program is considered the world’s first computer virus, and he is considered to be the theoretical «father» of computer virology.[13] In 1972, Veith Risak directly building on von Neumann’s work on self-replication, published his article «Selbstreproduzierende Automaten mit minimaler Informationsübertragung» (Self-reproducing automata with minimal information exchange).[14] The article describes a fully functional virus written in assembler programming language for a SIEMENS 4004/35 computer system. In 1980 Jürgen Kraus wrote his diplom thesis «Selbstreproduktion bei Programmen» (Self-reproduction of programs) at the University of Dortmund.[15] In his work Kraus postulated that computer programs can behave in a way similar to biological viruses.
The MacMag virus ‘Universal Peace’, as displayed on a Mac in March 1988
The Creeper virus was first detected on ARPANET, the forerunner of the Internet, in the early 1970s.[16] Creeper was an experimental self-replicating program written by Bob Thomas at BBN Technologies in 1971.[17] Creeper used the ARPANET to infect DEC PDP-10 computers running the TENEX operating system.[18] Creeper gained access via the ARPANET and copied itself to the remote system where the message, «I’M THE CREEPER. CATCH ME IF YOU CAN!» was displayed.[19] The Reaper program was created to delete Creeper.[20]
In 1982, a program called «Elk Cloner» was the first personal computer virus to appear «in the wild»—that is, outside the single computer or computer lab where it was created.[21] Written in 1981 by Richard Skrenta, a ninth grader at Mount Lebanon High School near Pittsburgh, it attached itself to the Apple DOS 3.3 operating system and spread via floppy disk.[21] On its 50th use the Elk Cloner virus would be activated, infecting the personal computer and displaying a short poem beginning «Elk Cloner: The program with a personality.»
In 1984 Fred Cohen from the University of Southern California wrote his paper «Computer Viruses – Theory and Experiments».[22] It was the first paper to explicitly call a self-reproducing program a «virus», a term introduced by Cohen’s mentor Leonard Adleman. In 1987, Fred Cohen published a demonstration that there is no algorithm that can perfectly detect all possible viruses.[23] Fred Cohen’s theoretical compression virus[24] was an example of a virus which was not malicious software (malware), but was putatively benevolent (well-intentioned). However, antivirus professionals do not accept the concept of «benevolent viruses», as any desired function can be implemented without involving a virus (automatic compression, for instance, is available under Windows at the choice of the user). Any virus will by definition make unauthorised changes to a computer, which is undesirable even if no damage is done or intended. The first page of Dr Solomon’s Virus Encyclopaedia explains the undesirability of viruses, even those that do nothing but reproduce.[25][26]
An article that describes «useful virus functionalities» was published by J. B. Gunn under the title «Use of virus functions to provide a virtual APL interpreter under user control» in 1984.[27] The first IBM PC compatible virus in the «wild» was a boot sector virus dubbed (c)Brain,[28] created in 1986 and was released in 1987 by Amjad Farooq Alvi and Basit Farooq Alvi in Lahore, Pakistan, reportedly to deter unauthorized copying of the software they had written.[29] The first virus to specifically target Microsoft Windows, WinVir was discovered in April 1992, two years after the release of Windows 3.0.[30] The virus did not contain any Windows API calls, instead relying on DOS interrupts. A few years later, in February 1996, Australian hackers from the virus-writing crew VLAD created the Bizatch virus (also known as «Boza» virus), which was the first known virus to target Windows 95. In late 1997 the encrypted, memory-resident stealth virus Win32.Cabanas was released—the first known virus that targeted Windows NT (it was also able to infect Windows 3.0 and Windows 9x hosts).[31]
Even home computers were affected by viruses. The first one to appear on the Amiga was a boot sector virus called SCA virus, which was detected in November 1987.[32]
DesignEdit
PartsEdit
A computer virus generally contains three parts: the infection mechanism, which finds and infects new files, the payload, which is the malicious code to execute, and the trigger, which determines when to activate the payload. [33]
- Infection mechanism
- Also called the infection vector, this is how the virus spreads. Some viruses have a search routine, which locate and infect files on disk.[34] Other viruses infect files as they are run, such as the Jerusalem DOS virus.
- Trigger
- Also known as a logic bomb, this is the part of the virus that determines the condition for which the payload is activated.[35] This condition may be a particular date, time, presence of another program, size on disk exceeding a threshold,[36] or opening a specific file.[37]
- Payload
- The payload is the body of the virus that executes the malicious activity. Examples of malicious activities include damaging files, theft of confidential information or spying on the infected system.[38][39] Payload activity is sometimes noticeable as it can cause the system to slow down or «freeze».[34] Sometimes payloads are non-destructive and their main purpose is to spread a message to as many people as possible. This is called a virus hoax.[40]
PhasesEdit
Virus phases is the life cycle of the computer virus, described by using an analogy to biology. This life cycle can be divided into four phases:
- Dormant phase
- The virus program is idle during this stage. The virus program has managed to access the target user’s computer or software, but during this stage, the virus does not take any action. The virus will eventually be activated by the «trigger» which states which event will execute the virus. Not all viruses have this stage.[34]
- Propagation phase
- The virus starts propagating, which is multiplying and replicating itself. The virus places a copy of itself into other programs or into certain system areas on the disk. The copy may not be identical to the propagating version; viruses often «morph» or change to evade detection by IT professionals and anti-virus software. Each infected program will now contain a clone of the virus, which will itself enter a propagation phase.[34]
- Triggering phase
- A dormant virus moves into this phase when it is activated, and will now perform the function for which it was intended. The triggering phase can be caused by a variety of system events, including a count of the number of times that this copy of the virus has made copies of itself.[34] The trigger may occur when an employee is terminated from their employment or after a set period of time has elapsed, in order to reduce suspicion.
- Execution phase
- This is the actual work of the virus, where the «payload» will be released. It can be destructive such as deleting files on disk, crashing the system, or corrupting files or relatively harmless such as popping up humorous or political messages on screen.[34]
Targets and replicationEdit
Computer viruses infect a variety of different subsystems on their host computers and software.[41] One manner of classifying viruses is to analyze whether they reside in binary executables (such as .EXE or .COM files), data files (such as Microsoft Word documents or PDF files), or in the boot sector of the host’s hard drive (or some combination of all of these).[42][43]
A memory-resident virus (or simply «resident virus») installs itself as part of the operating system when executed, after which it remains in RAM from the time the computer is booted up to when it is shut down. Resident viruses overwrite interrupt handling code or other functions, and when the operating system attempts to access the target file or disk sector, the virus code intercepts the request and redirects the control flow to the replication module, infecting the target. In contrast, a non-memory-resident virus (or «non-resident virus»), when executed, scans the disk for targets, infects them, and then exits (i.e. it does not remain in memory after it is done executing).[44]
Many common applications, such as Microsoft Outlook and Microsoft Word, allow macro programs to be embedded in documents or emails, so that the programs may be run automatically when the document is opened. A macro virus (or «document virus») is a virus that is written in a macro language and embedded into these documents so that when users open the file, the virus code is executed, and can infect the user’s computer. This is one of the reasons that it is dangerous to open unexpected or suspicious attachments in e-mails.[45][46] While not opening attachments in e-mails from unknown persons or organizations can help to reduce the likelihood of contracting a virus, in some cases, the virus is designed so that the e-mail appears to be from a reputable organization (e.g., a major bank or credit card company).
Boot sector viruses specifically target the boot sector and/or the Master Boot Record[47] (MBR) of the host’s hard disk drive, solid-state drive, or removable storage media (flash drives, floppy disks, etc.).[48]
The most common way of transmission of computer viruses in boot sector is physical media. When reading the VBR of the drive, the infected floppy disk or USB flash drive connected to the computer will transfer data, and then modify or replace the existing boot code. The next time a user tries to start the desktop, the virus will immediately load and run as part of the master boot record.[49]
Email viruses are viruses that intentionally, rather than accidentally, use the email system to spread. While virus infected files may be accidentally sent as email attachments, email viruses are aware of email system functions. They generally target a specific type of email system (Microsoft Outlook is the most commonly used), harvest email addresses from various sources, and may append copies of themselves to all email sent, or may generate email messages containing copies of themselves as attachments.[50]
DetectionEdit
To avoid detection by users, some viruses employ different kinds of deception. Some old viruses, especially on the DOS platform, make sure that the «last modified» date of a host file stays the same when the file is infected by the virus. This approach does not fool antivirus software, however, especially those which maintain and date cyclic redundancy checks on file changes.[51] Some viruses can infect files without increasing their sizes or damaging the files. They accomplish this by overwriting unused areas of executable files. These are called cavity viruses. For example, the CIH virus, or Chernobyl Virus, infects Portable Executable files. Because those files have many empty gaps, the virus, which was 1 KB in length, did not add to the size of the file.[52] Some viruses try to avoid detection by killing the tasks associated with antivirus software before it can detect them (for example, Conficker). A Virus may also hide its presence using a rootkit by not showing itself on the list of system processes or by disguising itself within a trusted process.[53] In the 2010s, as computers and operating systems grow larger and more complex, old hiding techniques need to be updated or replaced. Defending a computer against viruses may demand that a file system migrate towards detailed and explicit permission for every kind of file access.[citation needed]
Read request interceptsEdit
While some kinds of antivirus software employ various techniques to counter stealth mechanisms, once the infection occurs any recourse to «clean» the system is unreliable. In Microsoft Windows operating systems, the NTFS file system is proprietary. This leaves antivirus software little alternative but to send a «read» request to Windows files that handle such requests. Some viruses trick antivirus software by intercepting its requests to the operating system. A virus can hide by intercepting the request to read the infected file, handling the request itself, and returning an uninfected version of the file to the antivirus software. The interception can occur by code injection of the actual operating system files that would handle the read request. Thus, an antivirus software attempting to detect the virus will either not be permitted to read the infected file, or, the «read» request will be served with the uninfected version of the same file.[54]
The only reliable method to avoid «stealth» viruses is to boot from a medium that is known to be «clear». Security software can then be used to check the dormant operating system files. Most security software relies on virus signatures, or they employ heuristics.[55][56] Security software may also use a database of file «hashes» for Windows OS files, so the security software can identify altered files, and request Windows installation media to replace them with authentic versions. In older versions of Windows, file cryptographic hash functions of Windows OS files stored in Windows—to allow file integrity/authenticity to be checked—could be overwritten so that the System File Checker would report that altered system files are authentic, so using file hashes to scan for altered files would not always guarantee finding an infection.[57]
Self-modificationEdit
Most modern antivirus programs try to find virus-patterns inside ordinary programs by scanning them for so-called virus signatures.[58] Different antivirus programs will employ different search methods when identifying viruses. If a virus scanner finds such a pattern in a file, it will perform other checks to make sure that it has found the virus, and not merely a coincidental sequence in an innocent file, before it notifies the user that the file is infected. The user can then delete, or (in some cases) «clean» or «heal» the infected file. Some viruses employ techniques that make detection by means of signatures difficult but probably not impossible. These viruses modify their code on each infection. That is, each infected file contains a different variant of the virus.[citation needed]
One method of evading signature detection is to use simple encryption to encipher (encode) the body of the virus, leaving only the encryption module and a static cryptographic key in cleartext which does not change from one infection to the next.[59] In this case, the virus consists of a small decrypting module and an encrypted copy of the virus code. If the virus is encrypted with a different key for each infected file, the only part of the virus that remains constant is the decrypting module, which would (for example) be appended to the end. In this case, a virus scanner cannot directly detect the virus using signatures, but it can still detect the decrypting module, which still makes indirect detection of the virus possible. Since these would be symmetric keys, stored on the infected host, it is entirely possible to decrypt the final virus, but this is probably not required, since self-modifying code is such a rarity that finding some may be reason enough for virus scanners to at least «flag» the file as suspicious.[citation needed] An old but compact way will be the use of arithmetic operation like addition or subtraction and the use of logical conditions such as XORing,[60] where each byte in a virus is with a constant so that the exclusive-or operation had only to be repeated for decryption. It is suspicious for a code to modify itself, so the code to do the encryption/decryption may be part of the signature in many virus definitions.[citation needed] A simpler older approach did not use a key, where the encryption consisted only of operations with no parameters, like incrementing and decrementing, bitwise rotation, arithmetic negation, and logical NOT.[60] Some viruses, called polymorphic viruses, will employ a means of encryption inside an executable in which the virus is encrypted under certain events, such as the virus scanner being disabled for updates or the computer being rebooted.[61] This is called cryptovirology.
Polymorphic code was the first technique that posed a serious threat to virus scanners. Just like regular encrypted viruses, a polymorphic virus infects files with an encrypted copy of itself, which is decoded by a decryption module. In the case of polymorphic viruses, however, this decryption module is also modified on each infection. A well-written polymorphic virus therefore has no parts which remain identical between infections, making it very difficult to detect directly using «signatures».[62][63] Antivirus software can detect it by decrypting the viruses using an emulator, or by statistical pattern analysis of the encrypted virus body. To enable polymorphic code, the virus has to have a polymorphic engine (also called «mutating engine» or «mutation engine») somewhere in its encrypted body. See polymorphic code for technical detail on how such engines operate.[64]
Some viruses employ polymorphic code in a way that constrains the mutation rate of the virus significantly. For example, a virus can be programmed to mutate only slightly over time, or it can be programmed to refrain from mutating when it infects a file on a computer that already contains copies of the virus. The advantage of using such slow polymorphic code is that it makes it more difficult for antivirus professionals and investigators to obtain representative samples of the virus, because «bait» files that are infected in one run will typically contain identical or similar samples of the virus. This will make it more likely that the detection by the virus scanner will be unreliable, and that some instances of the virus may be able to avoid detection.
To avoid being detected by emulation, some viruses rewrite themselves completely each time they are to infect new executables. Viruses that utilize this technique are said to be in metamorphic code. To enable metamorphism, a «metamorphic engine» is needed. A metamorphic virus is usually very large and complex. For example, W32/Simile consisted of over 14,000 lines of assembly language code, 90% of which is part of the metamorphic engine.[65][66]
EffectsEdit
Damage is due to causing system failure, corrupting data, wasting computer resources, increasing maintenance costs or stealing personal information.[10] Even though no antivirus software can uncover all computer viruses (especially new ones), computer security researchers are actively searching for new ways to enable antivirus solutions to more effectively detect emerging viruses, before they become widely distributed.[67]
A power virus is a computer program that executes specific machine code to reach the maximum CPU power dissipation (thermal energy output for the central processing units). Computer cooling apparatus are designed to dissipate power up to the thermal design power, rather than maximum power, and a power virus could cause the system to overheat if it does not have logic to stop the processor. This may cause permanent physical damage. Power viruses can be malicious, but are often suites of test software used for integration testing and thermal testing of computer components during the design phase of a product, or for product benchmarking.[68]
Stability test applications are similar programs which have the same effect as power viruses (high CPU usage) but stay under the user’s control. They are used for testing CPUs, for example, when overclocking. Spinlock in a poorly written program may cause similar symptoms, if it lasts sufficiently long.
Different micro-architectures typically require different machine code to hit their maximum power. Examples of such machine code do not appear to be distributed in CPU reference materials.[69]
Infection vectorsEdit
As software is often designed with security features to prevent unauthorized use of system resources, many viruses must exploit and manipulate security bugs, which are security defects in a system or application software, to spread themselves and infect other computers. Software development strategies that produce large numbers of «bugs» will generally also produce potential exploitable «holes» or «entrances» for the virus.
To replicate itself, a virus must be permitted to execute code and write to memory. For this reason, many viruses attach themselves to executable files that may be part of legitimate programs (see code injection). If a user attempts to launch an infected program, the virus’ code may be executed simultaneously.[70] In operating systems that use file extensions to determine program associations (such as Microsoft Windows), the extensions may be hidden from the user by default. This makes it possible to create a file that is of a different type than it appears to the user. For example, an executable may be created and named «picture.png.exe», in which the user sees only «picture.png» and therefore assumes that this file is a digital image and most likely is safe, yet when opened, it runs the executable on the client machine.[71] Viruses may be installed on removable media, such as flash drives. The drives may be left in a parking lot of a government building or other target, with the hopes that curious users will insert the drive into a computer. In a 2015 experiment, researchers at the University of Michigan found that 45–98 percent of users would plug in a flash drive of unknown origin.[72]
The vast majority of viruses target systems running Microsoft Windows. This is due to Microsoft’s large market share of desktop computer users.[73] The diversity of software systems on a network limits the destructive potential of viruses and malware.[a] Open-source operating systems such as Linux allow users to choose from a variety of desktop environments, packaging tools, etc., which means that malicious code targeting any of these systems will only affect a subset of all users. Many Windows users are running the same set of applications, enabling viruses to rapidly spread among Microsoft Windows systems by targeting the same exploits on large numbers of hosts.[74][75][76][77]
While Linux and Unix in general have always natively prevented normal users from making changes to the operating system environment without permission, Windows users are generally not prevented from making these changes, meaning that viruses can easily gain control of the entire system on Windows hosts. This difference has continued partly due to the widespread use of administrator accounts in contemporary versions like Windows XP. In 1997, researchers created and released a virus for Linux—known as «Bliss».[78] Bliss, however, requires that the user run it explicitly, and it can only infect programs that the user has the access to modify. Unlike Windows users, most Unix users do not log in as an administrator, or «root user», except to install or configure software; as a result, even if a user ran the virus, it could not harm their operating system. The Bliss virus never became widespread, and remains chiefly a research curiosity. Its creator later posted the source code to Usenet, allowing researchers to see how it worked.[79]
Before computer networks became widespread, most viruses spread on removable media, particularly floppy disks. In the early days of the personal computer, many users regularly exchanged information and programs on floppies. Some viruses spread by infecting programs stored on these disks, while others installed themselves into the disk boot sector, ensuring that they would be run when the user booted the computer from the disk, usually inadvertently. Personal computers of the era would attempt to boot first from a floppy if one had been left in the drive. Until floppy disks fell out of use, this was the most successful infection strategy and boot sector viruses were the most common in the «wild» for many years. Traditional computer viruses emerged in the 1980s, driven by the spread of personal computers and the resultant increase in bulletin board system (BBS), modem use, and software sharing. Bulletin board–driven software sharing contributed directly to the spread of Trojan horse programs, and viruses were written to infect popularly traded software. Shareware and bootleg software were equally common vectors for viruses on BBSs.[80][81] Viruses can increase their chances of spreading to other computers by infecting files on a network file system or a file system that is accessed by other computers.[82]
Macro viruses have become common since the mid-1990s. Most of these viruses are written in the scripting languages for Microsoft programs such as Microsoft Word and Microsoft Excel and spread throughout Microsoft Office by infecting documents and spreadsheets. Since Word and Excel were also available for Mac OS, most could also spread to Macintosh computers. Although most of these viruses did not have the ability to send infected email messages, those viruses which did take advantage of the Microsoft Outlook Component Object Model (COM) interface.[83][84] Some old versions of Microsoft Word allow macros to replicate themselves with additional blank lines. If two macro viruses simultaneously infect a document, the combination of the two, if also self-replicating, can appear as a «mating» of the two and would likely be detected as a virus unique from the «parents».[85]
A virus may also send a web address link as an instant message to all the contacts (e.g., friends and colleagues’ e-mail addresses) stored on an infected machine. If the recipient, thinking the link is from a friend (a trusted source) follows the link to the website, the virus hosted at the site may be able to infect this new computer and continue propagating.[86] Viruses that spread using cross-site scripting were first reported in 2002,[87] and were academically demonstrated in 2005.[88] There have been multiple instances of the cross-site scripting viruses in the «wild», exploiting websites such as MySpace (with the Samy worm) and Yahoo!.
CountermeasuresEdit
In 1989 The ADAPSO Software Industry Division published Dealing With Electronic Vandalism,[89] in which they followed the risk of data loss by «the added risk of losing customer confidence.»[90][91][92]
Many users install antivirus software that can detect and eliminate known viruses when the computer attempts to download or run the executable file (which may be distributed as an email attachment, or on USB flash drives, for example). Some antivirus software blocks known malicious websites that attempt to install malware. Antivirus software does not change the underlying capability of hosts to transmit viruses. Users must update their software regularly to patch security vulnerabilities («holes»). Antivirus software also needs to be regularly updated to recognize the latest threats. This is because malicious hackers and other individuals are always creating new viruses. The German AV-TEST Institute publishes evaluations of antivirus software for Windows[93] and Android.[94]
Examples of Microsoft Windows anti virus and anti-malware software include the optional Microsoft Security Essentials[95] (for Windows XP, Vista and Windows 7) for real-time protection, the Windows Malicious Software Removal Tool[96] (now included with Windows (Security) Updates on «Patch Tuesday», the second Tuesday of each month), and Windows Defender (an optional download in the case of Windows XP).[97] Additionally, several capable antivirus software programs are available for free download from the Internet (usually restricted to non-commercial use).[98] Some such free programs are almost as good as commercial
competitors.[99] Common security vulnerabilities are assigned CVE IDs and listed in the US National Vulnerability Database. Secunia PSI[100] is an example of software, free for personal use, that will check a PC for vulnerable out-of-date software, and attempt to update it. Ransomware and phishing scam alerts appear as press releases on the Internet Crime Complaint Center noticeboard. Ransomware is a virus that posts a message on the user’s screen saying that the screen or system will remain locked or unusable until a ransom payment is made. Phishing is a deception in which the malicious individual pretends to be a friend, computer security expert, or other benevolent individual, with the goal of convincing the targeted individual to reveal passwords or other personal information.
Other commonly used preventive measures include timely operating system updates, software updates, careful Internet browsing (avoiding shady websites), and installation of only trusted software.[101] Certain browsers flag sites that have been reported to Google and that have been confirmed as hosting malware by Google.[102][103]
There are two common methods that an antivirus software application uses to detect viruses, as described in the antivirus software article. The first, and by far the most common method of virus detection is using a list of virus signature definitions. This works by examining the content of the computer’s memory (its Random Access Memory (RAM), and boot sectors) and the files stored on fixed or removable drives (hard drives, floppy drives, or USB flash drives), and comparing those files against a database of known virus «signatures». Virus signatures are just strings of code that are used to identify individual viruses; for each virus, the antivirus designer tries to choose a unique signature string that will not be found in a legitimate program. Different antivirus programs use different «signatures» to identify viruses. The disadvantage of this detection method is that users are only protected from viruses that are detected by signatures in their most recent virus definition update, and not protected from new viruses (see «zero-day attack»).[104]
A second method to find viruses is to use a heuristic algorithm based on common virus behaviors. This method can detect new viruses for which antivirus security firms have yet to define a «signature», but it also gives rise to more false positives than using signatures. False positives can be disruptive, especially in a commercial environment, because it may lead to a company instructing staff not to use the company computer system until IT services have checked the system for viruses. This can slow down productivity for regular workers.
Recovery strategies and methodsEdit
One may reduce the damage done by viruses by making regular backups of data (and the operating systems) on different media, that are either kept unconnected to the system (most of the time, as in a hard drive), read-only or not accessible for other reasons, such as using different file systems. This way, if data is lost through a virus, one can start again using the backup (which will hopefully be recent).[105] If a backup session on optical media like CD and DVD is closed, it becomes read-only and can no longer be affected by a virus (so long as a virus or infected file was not copied onto the CD/DVD). Likewise, an operating system on a bootable CD can be used to start the computer if the installed operating systems become unusable. Backups on removable media must be carefully inspected before restoration. The Gammima virus, for example, propagates via removable flash drives.[106][107]
Many websites run by antivirus software companies provide free online virus scanning, with limited «cleaning» facilities (after all, the purpose of the websites is to sell antivirus products and services). Some websites—like Google subsidiary VirusTotal.com—allow users to upload one or more suspicious files to be scanned and checked by one or more antivirus programs in one operation.[108][109] Additionally, several capable antivirus software programs are available for free download from the Internet (usually restricted to non-commercial use).[110] Microsoft offers an optional free antivirus utility called Microsoft Security Essentials, a Windows Malicious Software Removal Tool that is updated as part of the regular Windows update regime, and an older optional anti-malware (malware removal) tool Windows Defender that has been upgraded to an antivirus product in Windows 8.
Some viruses disable System Restore and other important Windows tools such as Task Manager and CMD. An example of a virus that does this is CiaDoor. Many such viruses can be removed by rebooting the computer, entering Windows «safe mode» with networking, and then using system tools or Microsoft Safety Scanner.[111] System Restore on Windows Me, Windows XP, Windows Vista and Windows 7 can restore the registry and critical system files to a previous checkpoint. Often a virus will cause a system to «hang» or «freeze», and a subsequent hard reboot will render a system restore point from the same day corrupted. Restore points from previous days should work, provided the virus is not designed to corrupt the restore files and does not exist in previous restore points.[112][113]
Microsoft’s System File Checker (improved in Windows 7 and later) can be used to check for, and repair, corrupted system files.[114] Restoring an earlier «clean» (virus-free) copy of the entire partition from a cloned disk, a disk image, or a backup copy is one solution—restoring an earlier backup disk «image» is relatively simple to do, usually removes any malware, and may be faster than «disinfecting» the computer—or reinstalling and reconfiguring the operating system and programs from scratch, as described below, then restoring user preferences.[105] Reinstalling the operating system is another approach to virus removal. It may be possible to recover copies of essential user data by booting from a live CD, or connecting the hard drive to another computer and booting from the second computer’s operating system, taking great care not to infect that computer by executing any infected programs on the original drive. The original hard drive can then be reformatted and the OS and all programs installed from original media. Once the system has been restored, precautions must be taken to avoid reinfection from any restored executable files.[115]
Popular cultureEdit
The first known description of a self-reproducing program in fiction is in the 1970 short story The Scarred Man by Gregory Benford which describes a computer program called VIRUS which, when installed on a computer with telephone modem dialing capability, randomly dials phone numbers until it hits a modem that is answered by another computer, and then attempts to program the answering computer with its own program, so that the second computer will also begin dialing random numbers, in search of yet another computer to program. The program rapidly spreads exponentially through susceptible computers and can only be countered by a second program called VACCINE.[116]
The idea was explored further in two 1972 novels, When HARLIE Was One by David Gerrold and The Terminal Man by Michael Crichton, and became a major theme of the 1975 novel The Shockwave Rider by John Brunner.[117]
The 1973 Michael Crichton sci-fi film Westworld made an early mention of the concept of a computer virus, being a central plot theme that causes androids to run amok.[118][better source needed] Alan Oppenheimer’s character summarizes the problem by stating that «…there’s a clear pattern here which suggests an analogy to an infectious disease process, spreading from one…area to the next.» To which the replies are stated: «Perhaps there are superficial similarities to disease» and, «I must confess I find it difficult to believe in a disease of machinery.»[119]
Other malwareEdit
The term «virus» is also misused by extension to refer to other types of malware. «Malware» encompasses computer viruses along with many other forms of malicious software, such as computer «worms», ransomware, spyware, adware, trojan horses, keyloggers, rootkits, bootkits, malicious Browser Helper Object (BHOs), and other malicious software. The majority of active malware threats are trojan horse programs or computer worms rather than computer viruses. The term computer virus, coined by Fred Cohen in 1985, is a misnomer.[120] Viruses often perform some type of harmful activity on infected host computers, such as acquisition of hard disk space or central processing unit (CPU) time, accessing and stealing private information (e.g., credit card numbers, debit card numbers, phone numbers, names, email addresses, passwords, bank information, house addresses, etc.), corrupting data, displaying political, humorous or threatening messages on the user’s screen, spamming their e-mail contacts, logging their keystrokes, or even rendering the computer useless. However, not all viruses carry a destructive «payload» and attempt to hide themselves—the defining characteristic of viruses is that they are self-replicating computer programs that modify other software without user consent by injecting themselves into the said programs, similar to a biological virus which replicates within living cells.
See alsoEdit
- Botnet
- Comparison of computer viruses
- Computer fraud and abuse act
- Computer security
- Crimeware
- Core Wars
- Cryptovirology
- Keystroke logging
- Malware
- Source code virus
- Spam (electronic)
- Technical support scam
- Trojan horse (computing)
- Virus hoax
- Windows 7 File Recovery
- Windows Action Center
- Zombie (computer science)
NotesEdit
- ^ This is analogous to how genetic diversity in a population decreases the chance of a single disease wiping out a population in biology.
ReferencesEdit
- ^ «The Internet comes down with a virus». The New York Times. August 6, 2014.
- ^
- Stallings, William (2012). Computer security : principles and practice. Boston: Pearson. p. 182. ISBN 978-0-13-277506-9.
- «Worm vs. Virus: What’s the Difference and Does It Matter?». Avast Academy. Avast Software s.r.o. Retrieved 9 March 2021.
- ^ Piqueira, Jose R.C.; de Vasconcelos, Adolfo A.; Gabriel, Carlos E.C.J.; Araujo, Vanessa O. (2008). «Dynamic models for computer viruses». Computers & Security. 27 (7–8): 355–359. doi:10.1016/j.cose.2008.07.006.
- ^
- Alan Solomon (2011-06-14). «All About Viruses». VX Heavens. Archived from the original on 2012-01-17. Retrieved 2014-07-17.
- Aycock, John (2006). Computer Viruses and Malware. Springer. p. 14. ISBN 978-0-387-30236-2.
- ^ «Worm vs. Virus: What’s the Difference and Does It Matter?». Avast Academy. Avast Software s.r.o. Retrieved 9 March 2021.
- ^ Yeo, Sang-Soo. (2012). Computer science and its applications : CSA 2012, Jeju, Korea, 22-25.11.2012. Springer. p. 515. ISBN 978-94-007-5699-1. OCLC 897634290.
- ^ Yu, Wei; Zhang, Nan; Fu, Xinwen; Zhao, Wei (October 2010). «Self-Disciplinary Worms and Countermeasures: Modeling and Analysis». IEEE Transactions on Parallel and Distributed Systems. 21 (10): 1501–1514. doi:10.1109/tpds.2009.161. ISSN 1045-9219. S2CID 2242419.
- ^
- Filiol, Eric (2005). Computer viruses: from theory to applications. Springer. p. 8. ISBN 978-2-287-23939-7.
- Harley, David; et al. (2001). Viruses Revealed. McGraw-Hill. p. 6. ISBN 0-07-222818-0.
- Ludwig, Mark A. (1996). The Little Black Book of Computer Viruses: Volume 1, The Basic Technologies. pp. 16–17. ISBN 0-929408-02-0.
- Aycock, John (2006). Computer Viruses and Malware. Springer. p. 27. ISBN 978-0-387-30236-2.
- ^ Bell, David J.; et al., eds. (2004). «Virus». Cyberculture: The Key Concepts. Routledge. p. 154. ISBN 9780203647059.
- ^ a b «Viruses that can cost you». Archived from the original on 2013-09-25.
- ^ Granneman, Scott. «Linux vs. Windows Viruses». The Register. Archived from the original on September 7, 2015. Retrieved September 4, 2015.
- ^ von Neumann, John (1966). «Theory of Self-Reproducing Automata» (PDF). Essays on Cellular Automata. University of Illinois Press: 66–87. Archived (PDF) from the original on June 13, 2010. Retrieved June 10, 2010.
- ^ Éric Filiol, Computer viruses: from theory to applications, Volume 1 Archived 2017-01-14 at the Wayback Machine, Birkhäuser, 2005, pp. 19–38 ISBN 2-287-23939-1.
- ^
Risak, Veith (1972), «Selbstreproduzierende Automaten mit minimaler Informationsübertragung», Zeitschrift für Maschinenbau und Elektrotechnik, archived from the original on 2010-10-05 - ^
Kraus, Jürgen (February 1980), Selbstreproduktion bei Programmen (PDF), archived from the original (PDF) on 2015-07-14, retrieved 2015-05-08 - ^ «Virus list». Archived from the original on 2006-10-16. Retrieved 2008-02-07.
- ^ Thomas Chen; Jean-Marc Robert (2004). «The Evolution of Viruses and Worms». Archived from the original on 2013-08-09. Retrieved 2009-02-16.
- ^ Parikka, Jussi (2007). Digital Contagions: A Media Archaeology of Computer Viruses. New York: Peter Lang. p. 50. ISBN 978-0-8204-8837-0. Archived from the original on 2017-03-16.
- ^ «The Creeper Worm, the First Computer Virus». History of information. Retrieved 16 June 2022.[unreliable source?]
- ^ Russell, Deborah; Gangemi, G.T. (1991). Computer Security Basics. O’Reilly. p. 86. ISBN 0-937175-71-4.
- ^ a b Anick Jesdanun (1 September 2007). «School prank starts 25 years of security woes». CNBC. Archived from the original on 20 December 2014. Retrieved April 12, 2013.
- ^ Cohen, Fred (1984), Computer Viruses – Theory and Experiments, archived from the original on 2007-02-18
- ^ Cohen, Fred, An Undetectable Computer Virus Archived 2014-05-25 at the Wayback Machine, 1987, IBM
- ^ Burger, Ralph, 1991. Computer Viruses and Data Protection, pp. 19–20
- ^ Alan Solomon; Dmitry O Gryaznov (1995). Dr. Solomon’s Virus Encyclopedia. Aylesbury, Buckinghamshire, U.K.: S & S International PLC. ISBN 1-897661-00-2.
- ^ Alan Solomon (2011-06-14). «All About Viruses». VX Heavens. Archived from the original on 2012-01-17. Retrieved 2014-07-17.
- ^ Gunn, J.B. (June 1984). «Use of virus functions to provide a virtual APL interpreter under user control». ACM SIGAPL APL Quote Quad Archive. ACM New York, NY, USA. 14 (4): 163–168. doi:10.1145/384283.801093. ISSN 0163-6006.
- ^ «Boot sector virus repair». Antivirus.about.com. 2010-06-10. Archived from the original on 2011-01-12. Retrieved 2010-08-27.
- ^ «Amjad Farooq Alvi Inventor of first PC Virus post by Zagham». YouTube. Archived from the original on 2013-07-06. Retrieved 2010-08-27.
- ^ «winvir virus». Archived from the original on 8 August 2016. Retrieved 10 June 2016.
- ^ Grimes, Roger (2001). Malicious Mobile Code: Virus Protection for Windows. O’Reilly. pp. 99–100. ISBN 9781565926820.
- ^ «SCA virus». Virus Test Center, University of Hamburg. 1990-06-05. Archived from the original on 2012-02-08. Retrieved 2014-01-14.
- ^ Ludwig, Mark (1998). The giant black book of computer viruses. Show Low, Ariz: American Eagle. p. 15. ISBN 978-0-929408-23-1.
- ^ a b c d e f Stallings, William (2012). Computer security : principles and practice. Boston: Pearson. p. 183. ISBN 978-0-13-277506-9.
- ^ Ludwig, Mark (1998). The giant black book of computer viruses. Show Low, Ariz: American Eagle. p. 292. ISBN 978-0-929408-23-1.
- ^ «Basic malware concepts» (PDF). cs.colostate.edu. Archived (PDF) from the original on 2016-05-09. Retrieved 2016-04-25.
- ^ Gregory, Peter (2004). Computer viruses for dummies. Hoboken, NJ: Wiley Pub. p. 210. ISBN 0-7645-7418-3.
- ^ «Payload». encyclopedia.kaspersky.com. Retrieved 2022-06-26.
- ^ «What is a malicious payload?». CloudFlare. Retrieved 2022-06-26.
{{cite web}}: CS1 maint: url-status (link) - ^ Szor, Peter (2005). The art of computer virus research and defense. Upper Saddle River, NJ: Addison-Wesley. p. 43. ISBN 0-321-30454-3.
- ^ Serazzi, Giuseppe; Zanero, Stefano (2004). «Computer Virus Propagation Models» (PDF). In Calzarossa, Maria Carla; Gelenbe, Erol (eds.). Performance Tools and Applications to Networked Systems. Lecture Notes in Computer Science. Vol. 2965. pp. 26–50. Archived (PDF) from the original on 2013-08-18.
- ^ Avoine, Gildas (2007). Computer System Security: Basic Concepts and Solved Exercises. EPFL Press / CRC Press. pp. 21–22. ISBN 9781420046205. Archived from the original on 2017-03-16.
- ^ Brain, Marshall; Fenton, Wesley (April 2000). «How Computer Viruses Work». HowStuffWorks.com. Archived from the original on 29 June 2013. Retrieved 16 June 2013.
- ^
- Polk, William T. (1995). Antivirus Tools and Techniques for Computer Systems. William Andrew (Elsevier). p. 4. ISBN 9780815513643. Archived from the original on 2017-03-16.
- Salomon, David (2006). Foundations of Computer Security. Springer. pp. 47–48. ISBN 9781846283413. Archived from the original on 2017-03-16.
- Grimes, Roger (2001). Malicious Mobile Code: Virus Protection for Windows. O’Reilly. pp. 37–38. ISBN 9781565926820.
- ^ Grimes, Roger (2001). «Macro Viruses». Malicious Mobile Code: Virus Protection for Windows. O’Reilly. ISBN 9781565926820.
- ^ Aycock, John (2006). Computer Viruses and Malware. Springer. p. 89. ISBN 9780387341880. Archived from the original on 2017-03-16.
- ^ «What is boot sector virus?». Archived from the original on 2015-11-18. Retrieved 2015-10-16.
- ^
- Skoudis, Edward (2004). «Infection mechanisms and targets». Malware: Fighting Malicious Code. Prentice Hall Professional. pp. 37–38. ISBN 9780131014053. Archived from the original on 2017-03-16.
- Anonymous (2003). Maximum Security. Sams Publishing. pp. 331–333. ISBN 9780672324598. Archived from the original on 2014-07-06.
- ^ Mishra, Umakant (2012). «Detecting Boot Sector Viruses- Applying TRIZ to Improve Anti-Virus Programs». SSRN Electronic Journal. doi:10.2139/ssrn.1981886. ISSN 1556-5068. S2CID 109103460.
- ^ Dave Jones. 2001 (December 2001). «Building an e-mail virus detection system for your network. Linux J. 2001, 92, 2-«.
- ^ Béla G. Lipták, ed. (2002). Instrument engineers’ handbook (3rd ed.). Boca Raton: CRC Press. p. 874. ISBN 9781439863442. Retrieved September 4, 2015.
- ^ «Computer Virus Strategies and Detection Methods» (PDF). Archived (PDF) from the original on 23 October 2013. Retrieved 2 September 2008.
- ^ «What is Rootkit – Definition and Explanation». www.kaspersky.com. 2022-03-09. Retrieved 2022-06-26.
- ^ Szor, Peter (2005). The Art of Computer Virus Research and Defense. Boston: Addison-Wesley. p. 285. ISBN 0-321-30454-3. Archived from the original on 2017-03-16.
- ^ Fox-Brewster, Thomas. «Netflix Is Dumping Anti-Virus, Presages Death Of An Industry». Forbes. Archived from the original on September 6, 2015. Retrieved September 4, 2015.
- ^ «How Anti-Virus Software Works». Stanford University. Archived from the original on July 7, 2015. Retrieved September 4, 2015.
- ^ «www.sans.org». Archived from the original on 2016-04-25. Retrieved 2016-04-16.
- ^ Jacobs, Stuart (2015-12-01). Engineering Information Security: The Application of Systems Engineering Concepts to Achieve Information Assurance. John Wiley & Sons. ISBN 9781119104711.
- ^ Bishop, Matt (2003). Computer Security: Art and Science. Addison-Wesley Professional. p. 620. ISBN 9780201440997. Archived from the original on 2017-03-16.
- ^ a b John Aycock (19 September 2006). Computer Viruses and Malware. Springer. pp. 35–36. ISBN 978-0-387-34188-0. Archived from the original on 16 March 2017.
- ^ «What is a polymorphic virus? — Definition from WhatIs.com». SearchSecurity. Retrieved 2018-08-07.
- ^ Kizza, Joseph M. (2009). Guide to Computer Network Security. Springer. p. 341. ISBN 9781848009165.
- ^ Eilam, Eldad (2011). Reversing: Secrets of Reverse Engineering. John Wiley & Sons. p. 216. ISBN 9781118079768. Archived from the original on 2017-03-16.
- ^ «Virus Bulletin : Glossary – Polymorphic virus». Virusbtn.com. 2009-10-01. Archived from the original on 2010-10-01. Retrieved 2010-08-27.
- ^ Perriot, Fredrick; Peter Ferrie; Peter Szor (May 2002). «Striking Similarities» (PDF). Archived (PDF) from the original on September 27, 2007. Retrieved September 9, 2007.
- ^ «Virus Bulletin : Glossary — Metamorphic virus». Virusbtn.com. Archived from the original on 2010-07-22. Retrieved 2010-08-27.
- ^ Kaspersky, Eugene (November 21, 2005). «The contemporary antivirus industry and its problems». SecureLight. Archived from the original on October 5, 2013.
- ^ Ganesan, Karthik; Jo, Jungho; Bircher, W. Lloyd; Kaseridis, Dimitris; Yu, Zhibin; John, Lizy K. (September 2010). «System-level max power (SYMPO)». Proceedings of the 19th international conference on Parallel architectures and compilation techniques — PACT ’10. p. 19. doi:10.1145/1854273.1854282. ISBN 9781450301787. S2CID 6995371. Retrieved 19 November 2013.
- ^ Thermal Performance Challenges from Silicon to Systems
- ^ «Virus Basics». US-CERT. Archived from the original on 2013-10-03.
- ^ «Virus Notice: Network Associates’ AVERT Discovers First Virus That Can Infect JPEG Files, Assigns Low-Profiled Risk». Archived from the original on 2005-05-04. Retrieved 2002-06-13.
- ^ «Users Really Do Plug in USB Drives They Find» (PDF).
- ^ «Operating system market share». netmarketshare.com. Archived from the original on 2015-05-12. Retrieved 2015-05-16.
- ^ Mookhey, K.K.; et al. (2005). Linux: Security, Audit and Control Features. ISACA. p. 128. ISBN 9781893209787. Archived from the original on 2016-12-01.
- ^ Toxen, Bob (2003). Real World Linux Security: Intrusion Prevention, Detection, and Recovery. Prentice Hall Professional. p. 365. ISBN 9780130464569. Archived from the original on 2016-12-01.
- ^ Noyes, Katherine (Aug 3, 2010). «Why Linux Is More Secure Than Windows». PCWorld. Archived from the original on 2013-09-01.
- ^ Raggi, Emilio; et al. (2011). Beginning Ubuntu Linux. Apress. p. 148. ISBN 9781430236276. Archived from the original on 2017-03-16.
- ^ «McAfee discovers first Linux virus» (Press release). McAfee, via Axel Boldt. 5 February 1997. Archived from the original on 17 December 2005.
- ^ Boldt, Axel (19 January 2000). «Bliss, a Linux ‘virus’«. Archived from the original on 14 December 2005.
- ^ David Kim; Michael G. Solomon (17 November 2010). Fundamentals of Information Systems Security. Jones & Bartlett Publishers. pp. 360–. ISBN 978-1-4496-7164-8. Archived from the original on 16 March 2017.
- ^ «1980s – Kaspersky IT Encyclopedia». Retrieved 2021-03-16.
- ^ «What is a Computer Virus?». Actlab.utexas.edu. 1996-03-31. Archived from the original on 2010-05-27. Retrieved 2010-08-27.
- ^ The Definitive Guide to Controlling Malware, Spyware, Phishing, and Spam. Realtimepublishers.com. 1 January 2005. pp. 48–. ISBN 978-1-931491-44-0. Archived from the original on 16 March 2017.
- ^ Eli B. Cohen (2011). Navigating Information Challenges. Informing Science. pp. 27–. ISBN 978-1-932886-47-4. Archived from the original on 2017-12-19.
- ^ Vesselin Bontchev. «Macro Virus Identification Problems». FRISK Software International. Archived from the original on 2012-08-05.
- ^ «Facebook ‘photo virus’ spreads via email». 2012-07-19. Archived from the original on 2014-05-29. Retrieved 2014-04-28.
- ^ Berend-Jan Wever. «XSS bug in hotmail login page». Archived from the original on 2014-07-04. Retrieved 2014-04-07.
- ^ Wade Alcorn. «The Cross-site Scripting Virus». bindshell.net. Archived from the original on 2014-08-23. Retrieved 2015-10-13.
- ^ Eugene H. Spafford; Kathleen A. Heaphy; David J. Ferbrache (1989). Dealing With Electronic Vandalism. ADAPSO Software Industry Division.
- ^ «Ka-Boom: Anatomy of a Computer Virus». InformationWeek. December 3, 1990. p. 60.
- ^ «Trove». trove.nla.gov.au.
- ^ Hovav, Anat (August 2005). «Capital market reaction to defective IT products». Computers and Security. 24 (5): 409–424. doi:10.1016/j.cose.2005.02.003.
- ^ «Detailed test reports—(Windows) home user». AV-Test.org. Archived from the original on 2013-04-07. Retrieved 2013-04-08.
- ^ «Detailed test reports — Android mobile devices». AV-Test.org. 2019-10-22. Archived from the original on 2013-04-07.
- ^ «Microsoft Security Essentials». Archived from the original on June 21, 2012. Retrieved June 21, 2012.
- ^ «Malicious Software Removal Tool». Microsoft. Archived from the original on June 21, 2012. Retrieved June 21, 2012.
- ^ «Windows Defender». Microsoft. Archived from the original on June 22, 2012. Retrieved June 21, 2012.
- ^ Rubenking, Neil J. (Feb 17, 2012). «The Best Free Antivirus for 2012». pcmag.com. Archived from the original on 2017-08-30.
- ^ Rubenking, Neil J. (Jan 10, 2013). «The Best Antivirus for 2013». pcmag.com. Archived from the original on 2016-04-25.
- ^ Rubenking, Neil J. «Secunia Personal Software Inspector 3.0 Review & Rating». PCMag.com. Archived from the original on 2013-01-16. Retrieved 2013-01-19.
- ^ «10 Step Guide to Protect Against Viruses». GrnLight.net. Archived from the original on 24 May 2014. Retrieved 23 May 2014.
- ^ «Google Safe Browsing». Archived from the original on 2014-09-14.
- ^ «Report malicious software (URL) to Google». Archived from the original on 2014-09-12.
- ^ Zhang, Yu; et al. (2008). «A Novel Immune Based Approach For Detection of Windows PE Virus». In Tang, Changjie; et al. (eds.). Advanced Data Mining and Applications: 4th International Conference, ADMA 2008, Chengdu, China, October 8-10, 2008, Proceedings. Springer. p. 250. ISBN 9783540881919. Archived from the original on 2017-03-16.
- ^ a b «Good Security Habits | US-CERT». Archived from the original on 2016-04-20. Retrieved 2016-04-16.
- ^ «W32.Gammima.AG». Symantec. Archived from the original on 2014-07-13. Retrieved 2014-07-17.
- ^ «Viruses! In! Space!». GrnLight.net. Archived from the original on 2014-05-24. Retrieved 2014-07-17.
{{cite web}}: CS1 maint: unfit URL (link) - ^ «VirusTotal.com (a subsidiary of Google)». Archived from the original on 2012-06-16.
- ^ «VirScan.org». Archived from the original on 2013-01-26.
- ^ Rubenking, Neil J. «The Best Free Antivirus for 2014». pcmag.com. Archived from the original on 2017-08-30.
- ^ «Microsoft Safety Scanner». Archived from the original on 2013-06-29.
- ^ «Virus removal -Help». Archived from the original on 2015-01-31. Retrieved 2015-01-31.
- ^ «W32.Gammima.AG Removal — Removing Help». Symantec. 2007-08-27. Archived from the original on 2014-08-04. Retrieved 2014-07-17.
- ^ «support.microsoft.com». Archived from the original on 2016-04-07. Retrieved 2016-04-16.
- ^ «www.us-cert.gov» (PDF). Archived (PDF) from the original on 2016-04-19. Retrieved 2016-04-16.
- ^ Benford, Gregory (May 1970). «The Scarred Man». Venture Science Fiction. Vol. 4, no. 2. pp. 122–.
- ^ Clute, John. «Brunner, John». The Encyclopedia of Science Fiction. Orion Publishing Group. Retrieved 30 January 2013.
- ^ IMDB synopsis of Westworld. Retrieved November 28, 2015.
- ^ Michael Crichton (November 21, 1973). Westworld (film). 201 S. Kinney Road, Tucson, Arizona, USA: Metro-Goldwyn-Mayer. Event occurs at 32 minutes.
And there’s a clear pattern here which suggests an analogy to an infectious disease process, spreading from one resort area to the next.» … «Perhaps there are superficial similarities to disease.» «I must confess I find it difficult to believe in a disease of machinery.
{{cite AV media}}: CS1 maint: location (link) - ^ Ludwig, Mark (1998). The giant black book of computer viruses. Show Low, Ariz: American Eagle. p. 13. ISBN 978-0-929408-23-1.
Further readingEdit
- Burger, Ralf (16 February 2010) [1991]. Computer Viruses and Data Protection. Abacus. p. 353. ISBN 978-1-55755-123-8.
- Granneman, Scott (6 October 2003). «Linux vs. Windows Viruses». The Register.
- Ludwig, Mark (1993). Computer Viruses, Artificial Life and Evolution. Tucson, Arizona 85717: American Eagle Publications, Inc. ISBN 0-929408-07-1. Archived from the original on July 4, 2008.
{{cite book}}: CS1 maint: location (link) - Mark Russinovich (November 2006). Advanced Malware Cleaning video (Web (WMV / MP4)). Microsoft Corporation. Retrieved 24 July 2011.
- Parikka, Jussi (2007). Digital Contagions. A Media Archaeology of Computer Viruses. Digital Formations. New York: Peter Lang. ISBN 978-0-8204-8837-0.
External linksEdit
- Viruses at Curlie (DMOZ)
- Microsoft Security Portal
- US Govt CERT (Computer Emergency Readiness Team) site
- ‘Computer Viruses – Theory and Experiments’ – The original paper by Fred Cohen, 1984
- Hacking Away at the Counterculture by Andrew Ross (On hacking, 1990)
Task
1. Read and translate the text:
Задание
1. Прочитайте
и
переведите
текст:
A
virus is a piece of software designed and written to adversely affect
your computer by altering the way. It works without your knowledge or
permission. In more technical terms, a virus is a segment of program
code that implants itself to one of your executable files and spreads
systematically from one file to another. Computer viruses do not
spontaneously generate. They must be written and have a
specific
purpose. Usually a virus has two distinct functions:
• Spreads
itself from one file to another without your input or knowledge.
Technically, this is known as self-replication and propagation.
• Implements
the symptom or damage planned by the perpetrator. This could include
erasing a disk, corrupting your programs or just creating havoc on
your computer. Technically, this is known as the virus payload, which
can be benign or malignant at the whim of the virus creator.
A
benign virus is
one that is designed to do no real damage to your computer. For
example, a virus that conceals itself until some predetermined date
or time and then does nothing more than display some sort of message
is considered benign.
A
malignant virus is
one that attempts to inflict malicious damage to your computer,
although the damage may not be intentional. There is a significant
number of viruses that cause damage due to poor programming and
outright bugs in the he viral code a high percentage of them are very
malignant. Some of the more malignant viruses will erase your entire
hard disk, or delete files.
A
malicious virus might
alter one or more of your programs so that it does not work, as it
should. The infected program might terminate abnormally, write
incorrect information into your documents. Or, the virus might after
the directory information on one of your system areas. This might
prevent the partition from mounting, or you might not be able to
launch one or more programs, or programs might not be able to locate
the documents you want to open.
What
Viruses
Do?
Some
viruses are programmed specifically to damage the data on your
computer by corrupting programs, deleting files, or erasing your
entire hard disk. Many of the currently known Macintosh viruses are
not designed to do any damage. However, because of bugs (programming
errors) within the virus, an infected system may behave erratically.
What
Viruses Don’t Do?
Computer
viruses don’t infect files on write-protected disks and don’t infect
documents, except in the case of Word macro viruses, which infect
only documents and templates written in Word 6.0 or higher. They
don’t infect compressed files either. However, applications within a
compressed file could have been infected before they were compressed.
Viruses also don’t infect computer hardware, such as monitors or
computer chips. They only infect software.
In
addition, Macintosh
viruses don’t
infect DOS-based computer software and vice versa. For example, the
infamous Michelangelo
virus does
not infect Macintosh applications. Exceptions to this rule are the
Word and Excel macro viruses, which infect spreadsheets, documents
and templates, which can be opened by either Windows or Macintosh
computers. Finally, viruses don’t necessarily let you know that they
are there — even after they do something destructive.
Types
of Computer Viruses.
Nowadays
number of viruses is about 55.000. It increases constantly. New
unknown types of viruses appear. To classify them becomes more and
more difficult. In common they can be divided by three basic signs: a
place of situating, used operation system and work algorithms. For
example, according to these three classifications virus
Chernobyl can
be classified as a file infector and resident Windows virus. Further
it will be explained what it means.
File
Infectors
These
are viruses that attach themselves to (or replace) COM and EXE files,
although in some cases they can infect files with extensions SYS,
DRV, BIN, OVL and OVY With this type of a virus, uninfected programs
usually become infected when they are executed with the virus in
memory. In other cases they are infected when they are opened (such
as using the DOS DIR command) or the virus simply infects all of the
files
in the directory is run from (a direct infector). There are three
groups of file infectors.
Viruses
of the first group are called overwriting
viruses because
they overwrite their code into an infected file erasing contents. But
these viruses are primitive and they can be found very quickly.
Oilier
group is called parasitic
or cavity viruses. The
infected file is capable of work fully or partly. Viruses can copy
itself into begin, middle or end of a file. They record their code in
data known not to be used.
The
third group is called companion
viruses. They
don’t change files. They make double of infected file so when an
infected file is being started a double file becomes managing, it
means a virus. For example, companion viruses working with DOS use
that DOS firstly runs COM. file. Viruses make double file with the
same name and with extension COM and copies
itself
in this file. During start of an infected file DOS run
a
COM. file with a virus firstly and then a virus starts an
EXE
file.
Sometimes
companion
viruses rename
file will be infected and record their code in a double file with old
name. For example, the file XCOPY.EX is renamed into XCOPY.EXD and a
virus record itself in file XCOPY.EXE. When this file is started
computer runs a virus code firstly and after the virus starts
original XCOPY, saved as XCOPY.EXD. Viruses like these ones were
found not only in DOS. They were found in Windows and OS / 2.
It
is not only one way to make double files. For example there is a
subgroup of companion viruses called path-companion viruses. They use
special feature of DOS-PATH: hierarchical record of file location.
The virus copies itself in a file with the same name but situated one
level higher. In this case DOS will find a file with a virus.
Task
2. Answer the following questions:
Задание
2. Ответьте
на следующие вопросы:
-
What
is a computer virus? -
How
many types of viruses are there? What are they? -
How
many groups of file-Infector do you know? -
What
do companion viruses do? -
What
don’t viruses do? -
What
do special feature of POS path-companion viruses use? -
Computer
viruses do spontaneously generate, don’t they? -
What
viruses will erase your entire hard disk? -
How
are viruses divided? -
Viruses
don’t necessarily let you know that they are there-even after they
do
something destructive, do they?
Task
3. Match the English words given below with their Russian
equivalents:
Задание
3. Соотнесите следующие слова с
соответствующим переводом:
|
• a
• a • software
• direct
• a
• an
• a
• a • destructive
• a
• a
• executable
• a
• a
• a
• a
• compressed
• a
• macro
• erasing
• a
• an
• a
• a |
• файл-инфектор • повреждать
• жесткий
• злостный • монитор
• компьютерный
• программная
• неопасный • симптом
• программное • макровирус
• вирусный
• место
• главный
• сжатые
• зараженная
• резидентный • самоответ
• исполнительные • разрушение
• стирающий
• алгоритм
• компьютерные • приложение |
Task
4. Find the sentences with the words and word
— combinations
given below in the text:
Задание
4. Найдите в тексте предложения, содержащие
нижеследующие слова и выражения:
• a
segment of program code
• executable
files
• a
virus payload
• a
viral code
• a
partition from mounting
• DOS
— based computer software
• Word
and Excel macro viruses
• to
make double of infected file
Task
5. Complete the following sentences corresponding to the contents of
the text:
Задание
5.
Закончите
предложения:
-
Other
group is called … -
The
third group is called … . -
Usually
a virus has two distinct functions … . -
Computer
viruses do not …
. -
Sometime
companion viruses rename file will be. -
Virus
copies itself in …
. -
Chernobyl
can be … . -
Viruses
also don’t ….
. -
They
must be ….. . -
Viruses
of the first group are called … . -
A
virus is a piece of … . -
This
could include erasing a disk … on your computer. -
Some
viruses programmed … your entire hard disk. -
…
on write-protected disks and … in the case of …. . -
These
are viruses that …
.
Task
6. Say whether the statements given below are true or false:
Задание
6. Определите истинность или ложность
следующих предложений:
1.
Some of the more malignant viruses will erase your entire hard disk,
or delete files.
2.
Computer viruses do infect files on write-protected disks and do
infect documents, except in the case of Word macro viruses, which
infect only documents and templates written in Word 6.0 or higher.
3.
Usually a virus has six distinct functions.
4.
There are many groups of file infectors.
5.
Nowadays number of viruses is about 55.000.
6.
Other group is called parasitic or overwriting viruses.
7.
Viruses also don’t infect computer hardware such as monitors or
computer chips; they only infect software.
8.
Virus is a software designed and written to adversely affect your
computer.
9.
Viruses didn’t spontaneously generate.
10.
A malignant virus is one that is designed to do no real damage to
your computer.
11.
A benign virus might alter one or two of your programs so that it
doesn’t work, as it should.
12.
The infected programs second of you system area.
13.
In
addition, Macintosh virus doesn’t infect DOS — based computer
software and vice versa.
14.
Finally, viruses don’t necessarily let you know that they are there —
even after do something destructive.
15.
In
this case DOS wasn’t find file with virus.
Task
7. Translate from Russian into Englis:
Задание
7. Переведите с русского языка на
английский:
1.
Что такое компьютерный вирус?
2.
Вирус — это часть программного
обеспечения, написанного для того, чтобы
неблагоприятно влиять на ваш компьютер,
изменяя его работу без вашего ведома и
согласия.
3.
Вирус имеет две отличительные функции:
нанесение запланированного ущерба и
самораспространение.
4.
Существуют безвредные вирусы и вирусы,
наносящие большой ущерб компьютеру.
5.
Вирусы могут повредить данные, изменить
программы, удалить файлы, стереть жесткий
диск.
6.
Вирусы не инфицируют файлы на пишущихся
защищенных дисках.
7.
В настоящее время вирусов около 55.000.
8.
Появляются новые, неизвестные типы
вирусов, которые становятся все сложнее
классифицировать.
9.
Есть 3 группы вирусов: 1) всепишущие, 2)
вирусы-паразиты, 3) вирусы-компаньоны.
10.
Установка
антивирусных программ позволяет находить
и удалять вирусы.
Task
8. Make the sentences negative and interrogative:
Задание
8. Преобразуйте следующие предложения
в вопросительную и отрицательную форму:
1.
A virus is a piece of software.
2.
This is a significant number of viruses.
3.
A malicious virus might alter one or more of your program.
4.
Some viruses are programmed specifically to damage the data on your
computer programs.
5.
Computer viruses infect files on write-protected disks.
6.
Number of viruses is about 55.000.
7.
These are three groups of file infectors.
8.
Viruses can copy itself into begin, middle or end of a file.
9.
This is a subgroup of companion viruses path — companion viruses.
10.
Virus copies itself in a file.
LESSON
16
Соседние файлы в предмете [НЕСОРТИРОВАННОЕ]
- #
- #
- #
10.06.20151.78 Mб542.doc
- #
10.06.2015138.38 Кб652.docx
- #
- #
- #
- #
- #
- #
- #
A computer virus is a variety of malicious code or program crafted to alter normal computer operations and spread through self-replication. The virus attaches to a program or file, lying in wait until you run the infected source, thereby executing the malicious code.
From there, the computer virus may steal passwords, log keystrokes, spam email contacts, corrupt or destroy data, damage programs, reformat the hard drive, and/or slow normal functions.
In short, a computer virus acts much like any other virus. It does damage. It spreads from host to host. And its villainous rampage must be stopped in order to return to normalcy.
We’ll explain what you should know about computer viruses, how they impact businesses, and what you can do to prevent and detect them.
What is the difference between a computer virus and malware?
A computer virus is a type of malware, but not all malware qualifies as a computer virus. The term malware encompasses any and all malicious software. However, for malware to be considered a virus, it must insert itself into another program and self-replicate.
Other types of malware can be just as devastating as viruses. We’ll break down some of the most common variations.
Types of malware
-
Virus: A computer virus inserts code into an application, program, file, or system and spreads copies of itself when triggered.
-
Fileless malware: Fileless malware alters files native to the operating system to appear legitimate and evade detection.
-
Rootkit: A rootkit is a clandestine malicious program that gives threat actors a backdoor into your computer.
-
Trojan: A Trojan, also known as a Trojan horse, is malicious software that looks legitimate to trick users into executing it.
-
Worm: Like viruses, worms are self-replicating malware. However, they’re not dependent on a host, and they don’t need to be triggered by a user action.
-
Spyware: Keyloggers and other forms of spyware collect activity data, which can be used to steal credentials or collect other sensitive information.
-
Ransomware: Ransomware encrypts files, effectively holding them hostage until a ransom is paid.
-
Adware: Adware collects personal information and displays unwanted ads.
What are the different types of computer viruses?
Hackers utilize a wide array of computer viruses, and new viruses emerge regularly. No one ever said cybersecurity was easy. Let’s bemoan a few common viruses:
Polymorphic virus: By regularly mutating, these viruses nimbly avoid detection.
Multipartite virus: This computer virus simultaneously infects the boot sector and files, performing unauthorized actions to spread.
Boot sector virus: Often transmitted via a malicious USB drive, this virus typically targets the Master Boot Record.
File infector: Also known as a file-infecting virus, a file infector generally attaches to executable files or command extensions.
-
Resident virus: A resident virus lives in your RAM and interferes with your operating system.
-
Direct action virus: A direct action virus targets a specific file type (usually executable files) and activates when an infected file is opened.
Browser hijacker: As the name suggests, a browser hijacker redirects your browser to malicious websites.
Web scripting virus: Hiding in the coding of links, images, ads, videos, and websites, a web scripting virus can infect systems through downloads or visits to an infected website.
Network virus: A network virus travels through the network and replicates via network packets.
Macro virus: Often transmitted via an infected Microsoft Word or Excel file, macro viruses are written in the same macro language as the software and frequently spread through email attachments.
Overwrite virus: This computer virus overwrites file content with its own code to destroy system elements.
How do computer viruses impact businesses?
Computer viruses affect businesses in innumerable ways, but they’re particularly damaging to operations, finances, and reputation.
Interruption of normal operations
A computer virus can bring your day-to-day operations to a grinding halt. Between lost data and disabled computer systems, you may not be able to maintain the consistency your customers and clients rely on. While your IT team scrambles to restore backups, other employees may be left sitting on their hands, unable to perform their jobs without essential resources.
Financial damage
Calculating the true cost of a computer virus is nearly impossible. That said, there’s no doubt that the financial damage can be devastating. If left unchecked, a virus can lead to a full-scale data breach, which costs an average of $4.24 million per incident.
Many industries are also subject to cybersecurity compliance requirements. Experiencing a cybersecurity incident may point to violations that could result in hefty fines.
Reputation damage
If a virus infection interrupts normal operations or puts private information at risk, you may have no choice but to disclose it to clients and customers. While cybercriminals may target any business, succumbing to an attack can do irreparable harm to your reputation. With reputation accounting for 63% of a company’s market value, the reputational damage can continue to harm your business for years to come.
How can you prevent computer viruses at your company?
Preventing computer viruses can save your business time, money, and hangover-level headaches. With a few simple techniques, you can dodge those bullets like you’re in “The Matrix.”
Train employees
All too often, well-meaning employees inadvertently introduce a virus into your environment. Viruses and other malware are frequently transmitted through suspicious links or email attachments. Phishing emails may appear legitimate on the surface, making detection all the more complicated.
If your employees don’t know what to look for, they may be more susceptible to the tricks of cybercriminals, exposing your business to risk. Equipping your staff with the knowledge and skills to recognize the early signs of an attack attempt turns them into your first line of defense.
Use a firewall
A firewall is like the drawbridge of a castle. If the king’s friends arrive for mead and merriment, the castle guards lower the drawbridge to let them in. But if a band of well-armed barbarians shows up, you better bet that drawbridge is staying as closed as a Blockbuster store.
Similarly, a firewall blocks your internal business network from unwelcome external users, blocks access to unapproved websites, and blocks malicious applications. Some things may still sneak through, but a good firewall makes a cybercriminal’s job much more complicated.
Install antivirus software
When malware makes it past the firewall, antivirus software lies in wait to intercept it. Virus protection software is designed to detect and remove several varieties of malware, including viruses, Trojans, rootkits, spyware, and more.
Deploy updates and patches quickly
Updates and patches address newly discovered vulnerabilities that cybercriminals look to exploit. When developers announce a new patch or update, savvy threat actors often act quickly to take advantage before businesses have time to protect themselves. In fact, a study by Ponemon Institute and ServiceNow found that 60% of breaches occurred due to an unpatched known vulnerability. Rapid deployment can be a gamechanger in keeping your systems safe, which is why PDQ Deploy is a good sidekick for all your quests. It makes deployment quick and painless.
How can you tell if your network or computer has a virus?
Virus-infected computers typically show telltale symptoms. Recognizing the signs that a device is compromised can help you address the problem more quickly, limiting dwell time.
Watch for the following indications:
-
Frequent crashes, blue screens, or error messages
-
Slow performance
-
Unknown programs starting
-
Unknown apps appearing
-
Popups with links to malicious websites
-
Browser homepage changes
-
Password changes
-
Suspicious messages sent from your account
-
Computer fan runs more often
-
Antivirus software and/or firewalls malfunction
If you’ve noticed any of these signs that your computer may be infected, contact your company’s IT department to detect and remove the virus.
How can you detect computer viruses?
A virus scanner or a threat detection service can help you pinpoint viruses in your environment.
Scanners are a critical component of antivirus software. They check your memory, boot sector, and disk for potential signs of viruses. Should the scanner find a suspected virus, it will quarantine it, delete it, or disinfect it.
Threat detection services typically take it a step further by leveraging human expertise and analytics to identify more advanced threats.
Virus scanners and threat detection services can use several types of detection methods:
-
Signature-based detection: Looks for digital fingerprints consistent with the patterns of known attacks
-
Behavioral detection: Uncovers unknown threats by evaluating code to analyze its potential actions
-
Cloud-based detection: Maintains threat definitions in the cloud to free up space and provide real-time protection against the latest threats
How do you choose the right antivirus software for your business?
Selecting the right antivirus software for your business requires weighing your needs against the software’s features. There are countless quality options on the market, and each carries distinct potential benefits and drawbacks.
Questions to consider
Asking yourself the following questions can help you narrow down your choices for antivirus software:
-
What devices and operating systems does it support?
-
What features do you really need?
-
How many devices do you need to protect?
-
How much does it cost?
-
Is there after-sales support?
Antivirus software features
Antivirus software solutions have features intended to enhance your overall cybersecurity posture. However, some components can increase the cost without necessarily improving the value for your business. Understanding the standard features of antivirus software makes it easier to weigh what your company truly needs.
Prevention & Detection
Prevention and detection are at the heart of all antivirus software solutions. They aim to stop viruses from infecting your computer and detect those already in your environment for rapid remediation. Key features that work towards these goals include:
-
Reactive file scanning: Scans each file to evaluate risks before opening or downloading it
-
System scanning: Scans the full device for signs of compromise
-
Real-time scanning: Provides protection as you use the computer
-
Web browsing protection: Scans URLs and web pages and let you know whether they’re safe to visit
-
Firewalls: Filters network traffic
-
Vulnerability detection: Scans for known exploitable vulnerabilities
-
Scan scheduling: Performs routine scans on your schedule
-
Spam & anti-phishing protection: Identifies emails that may contain malicious attachments and URLs
Removal
Once it detects a virus, the antivirus software should be able to stop it from damaging your computer. Common removal methods include:
-
Quarantining: Moves potentially malicious files to a safe folder so that you can review them
-
Auto-cleaning: Cleans infected files automatically
Other features
Antivirus software often comes with additional features. While they may not be essential to prevention, detection, and removal, they can provide added value.
-
Automatic updating: Installs updates automatically to stay current
-
Data & traffic encryption: Encrypts data and traffic to protect privacy
-
Cloud backup: Copies files to the cloud in case they are lost or stolen
-
Secure browser: Includes extra security features for safer browsing
-
Secure deletion of files: Removes files and prevents recovery
-
Password manager: Generates, manages, and stores passwords
-
System optimization: Detects and cleans unnecessary files
-
VPN service: Encrypts data and hides your activity
-
Data leak monitoring: Notifies you of leaked data
Features vary between antivirus solutions, but at a bare minimum, you should look for the following:
-
High-quality known threat database: To protect against the latest threats, antivirus software needs a comprehensive and current known threat database. Without it, your environment may not be as secure as you think.
-
Good detection rates: For a solution to work, it must limit false positives and false negatives. False positives alert to non-malicious activity, wasting time and resources. False negatives can be even more devastating, failing to identify a true threat and leaving you open to a cybersecurity incident.
-
Runs well without slowing performance: Antivirus software should be able to perform quietly in the background without causing significant lag.
-
Easy to use: With so many convenient solutions on the market, there’s no need to use a lot of time and effort to operate your antivirus software. An intuitive interface and automatic updates make antivirus software easier to use.
How do you deal with computer viruses?
Once you realize you may have a computer virus, you should aim to remove it as quickly as possible to limit the amount of time that threat actors have in your environment. If you’re using a PC, these 10 easy steps usually nip the virus in the bud.
1. Get high-quality paid antivirus software
While free options are widely available, paid software typically has more robust features. Ideally, you should use a paid solution at all times, but it is especially important to invest in quality if you suspect you already have a virus in your computer system.
2. Disconnect from the internet
Since some computer viruses use your internet connection to proliferate, you may want to disconnect the affected machine from the internet to protect other connected devices.
3. Reboot in safe mode
Using safe mode helps protect your device while you battle the virus.
If your operating system is Microsoft Windows 8.1 or later, follow these steps:
-
Click the start button, then the power icon
-
Hold down the shift key, and press “Restart”
-
Select “Troubleshoot,” then “Advanced Options,” then “Startup Settings”
-
Click “Restart”
-
Your computer will restart and show you a “Startup Settings” menu; select “Enable Safe Mode with Networking”
4. Delete temporary files
Since some viruses launch when your computer boots, delete temporary internet files as a precaution.
To do this:
-
Type “Disk Cleanup” in the Windows search bar and open the app
-
Check “Temporary internet files” and “Temporary files”
-
Click “Clean up system files”
5. Run a full system scan
Using your high-quality, paid antivirus software, run a full system scan. This may take several hours.
6. Delete or quarantine any detected virus
Once the scan is complete, delete or quarantine malicious files.
7. Rescan your computer
After removing any threats detected in the initial scan, scan again to confirm that the malware was successfully removed and that there are no lingering remnants of virus code.
8. Reboot your computer
With the virus removed, reboot your computer out of safe mode.
9. Change passwords
When the virus was on your computer, passwords may have been compromised. To be safe, change any important passwords. If you prefer to skip this step, check the virus’s functionality through the antivirus software page or the technical support team. If you can confirm it didn’t collect credentials or log keystrokes, changing passwords may be unnecessary.
10. Update software
Update and patch all software and apps on your computer, including the operating system and browser. This helps address known vulnerabilities to prevent threat actors from infiltrating your environment. Continue to update regularly for a better overall cybersecurity posture.
Every day, computer viruses devastate businesses. And all too often, they’re preventable. Keeping your machines up to date is one of the easiest ways to reduce the risk of a virus hurting your business’s bottom line and reputation.
Looking to streamline your patch management
and software deployment processes?
June 18, 2020 | By admin

Loading…
A computer virus is a malicious program that self-replicates by copying itself to another program. In other words, the computer virus spreads by itself into other executable code or documents. The purpose of creating a computer virus is to infect vulnerable systems, gain admin control and steal user sensitive data. Hackers design computer viruses with malicious intent and prey on online users by tricking them.
One of the ideal methods by which viruses spread is through emails – opening the attachment in the email, visiting an infected website, clicking on an executable file, or viewing an infected advertisement can cause the virus to spread to your system. Besides that, infections also spread while connecting with already infected removable storage devices, such as USB drives.
It is quite easy and simple for the viruses to sneak into a computer by dodging the defense systems. A successful breach can cause serious issues for the user such as infecting other resources or system software, modifying or deleting key functions or applications and copy/delete or encrypt data.
A computer virus operates in two ways. The first kind, as soon as it lands on a new computer, begins to replicate. The second type plays dead until the trigger kick starts the malicious code. In other words, the infected program needs to run to be executed. Therefore, it is highly significant to stay shielded by installing a robust antivirus program.
Of late, the sophisticated computer virus comes with evasion capabilities that help in bypassing antivirus software and other advanced levels of defenses. The primary purpose can involve stealing passwords or data, logging keystrokes, corrupting files, and even taking control of the machine.
Subsequently, the polymorphic malware development in recent times enables the viruses to change its code as it spreads dynamically. This has made the virus detection and identification very challenging.
Robert Thomas, an engineer at BBN Technologies developed the first known computer virus in the year 1971. The first virus was christened as the “Creeper” virus, and the experimental program carried out by Thomas infected mainframes on ARPANET. The teletype message displayed on the screens read, “I’m the creeper: Catch me if you can.”
But the original wild computer virus, probably the first one to be tracked down in the history of computer viruses was “Elk Cloner.” The Elk Cloner infected Apple II operating systems through floppy disks. The message displayed on infected Apple Computers was a humorous one. The virus was developed by Richard Skrenta, a teenager in the year 1982. Even though the computer viruses were designed as a prank, it also enlightened how a malicious program could be installed in a computer’s memory and stop users from removing the program.
It was Fred Cohen, who coined the term “computer virus” and it was after a year in 1983. The term came into being when he attempted to write an academic paper titled “Computer Viruses – Theory and Experiments” detailing about the malicious programs in his work.
Types of Computer Viruses
A computer virus is one type of malware that inserts its virus code to multiply itself by altering the programs and applications. The computer gets infected through the replication of malicious code. Computer viruses come in different forms to infect the system in different ways. Find some of the most common type of computer viruses here,
- Boot Sector Virus
- Direct Action Virus
- Resident Virus
- Multipartite Virus
- Polymorphic Virus
- Overwrite Virus
- Spacefiller Virus
Boot Sector Virus – This type of virus infects the master boot record and it is challenging and a complex task to remove this virus and often requires the system to be formatted. Mostly it spreads through removable media.
Direct Action Virus – This is also called non-resident virus, it gets installed or stays hidden in the computer memory. It stays attached to the specific type of files that it infect. It does not affect the user experience and system’s performance.
Resident Virus – Unlike direct action viruses, resident viruses get installed on the computer. It is difficult to identify the virus and it is even difficult to remove a resident virus.
Multipartite Virus – This type of virus spreads through multiple ways. It infects both the boot sector and executable files at the same time.
Polymorphic Virus – These type of viruses are difficult to identify with a traditional anti-virus program. This is because the polymorphic viruses alters its signature pattern whenever it replicates.
Overwrite Virus – This type of virus deletes all the files that it infects. The only possible mechanism to remove is to delete the infected files and the end-user has to lose all the contents in it. Identifying the overwrite virus is difficult as it spreads through emails.
Spacefiller Virus – This is also called “Cavity Viruses”. This is called so as they fill up the empty spaces between the code and hence does not cause any damage to the file.
#File infectors:
Few file infector viruses come attached with program files, such as .com or .exe files. Some file infector viruses infect any program for which execution is requested, including .sys, .ovl, .prg, and .mnu files. Consequently, when the particular program is loaded, the virus is also loaded.
Besides these, the other file infector viruses come as a completely included program or script sent in email attachments.
#Macro viruses:
As the name suggests, the macro viruses particularly target macro language commands in applications like Microsoft Word. The same is implied on other programs too.
In MS Word, the macros are keystrokes that are embedded in the documents or saved sequences for commands. The macro viruses are designed to add their malicious code to the genuine macro sequences in a Word file. However, as the years went by, Microsoft Word witnessed disabling of macros by default in more recent versions. Thus, the cybercriminals started to use social engineering schemes to target users. In the process, they trick the user and enable macros to launch the virus.
Since macro viruses are making a come back in the recent years, Microsoft quickly retaliated by adding a new feature in Office 2016. The feature enables security managers to selectively enable macro use. As a matter of fact, it can be enabled for trusted workflows and blocked if required across the organization.
#Overwrite Viruses:
The virus design purpose tends to vary and Overwrite Viruses are predominantly designed to destroy a file or application’s data. As the name says it all, the virus after attacking the computer starts overwriting files with its own code. Not to be taken lightly, these viruses are more capable of targeting specific files or applications or systematically overwrite all files on an infected device.
On the flipside, the overwrite virus is capable of installing a new code in the files or applications which programs them to spread the virus to additional files, applications, and systems.
#Polymorphic Viruses:
More and more cybercriminals are depending on the polymorphic virus. It is a malware type which has the ability to change or mutate its underlying code without changing its basic functions or features. This helps the virus on a computer or network to evade detection from many antimalware and threat detection products.
Since virus removal programs depend on identifying signatures of malware, these viruses are carefully designed to escape detection and identification. When a security software detects a polymorphic virus, the virus modifies itself thereby, it is no longer detectable using the previous signature.
#Resident Viruses:
The Resident virus implants itself in the memory of a computer. Basically, the original virus program is not required to infect new files or applications. Even when the original virus is deleted, the version stored in memory can be activated. This happens when the computer OS loads certain applications or functions. The resident viruses are troublesome due to the reason they can run unnoticed by antivirus and antimalware software by hiding in the system’s RAM.
#Rootkit Viruses:
The rootkit virus is a malware type which secretly installs an illegal rootkit on an infected system. This opens the door for attackers and gives them full control of the system. The attacker will be able to fundamentally modify or disable functions and programs. Like other sophisticated viruses, the rootkit virus is also created to bypass antivirus software. The latest versions of major antivirus and antimalware programs include rootkit scanning.
#System or Boot-record Infectors:
The Boot-record Infectors infect executable code found in specific system areas on a disk. As the name implies, they attach to the USB thumb drives and DOS boot sector on diskettes or the Master Boot Record on hard disks. Boot viruses are no more common these days as the latest devices rely less on physical storage media.
How To Avoid Email Viruses And Worms
Here are some simple rules you can follow to avoid being infected by viruses through email.
How To Be Safe From Email Viruses And Worms
Here are some simple rules you can follow to avoid being infected by viruses through email.
Do’s
1. Use a professional, email service such as Runbox. Subscription services provide higher levels of security and support.
2. Make sure that your Runbox virus filter is activated.
3. Use the Webmail interface at www.runbox.com to read your email, or don’t download all your email to an email client unseen. Screen your email first, and delete suspicious-looking and unwanted messages before downloading the legitimate email to your local email client.
4. Make sure your computer has updated anti-virus software running locally. Automatic updates are essential for effective virus protection. Combined with server-side scanning, you now have two layers of security.
5. Disable message preview in your email client, especially on Windows platforms. Otherwise, malicious programs attached to incoming messages may execute automatically and infect your computer.
6. Ignore or delete messages with attachments appearing to be sent from official Runbox email addresses. Runbox rarely sends email to our users, aside from replies to inquiries and payment reminders. We practically never send an email with attachments to users.
7. Take caution when opening graphics and media attachments, as viruses can be disguised as such files.
8. Maintain several independent email accounts. If a virus infects your only business email address, you’ll be in trouble. Also, keep backups of your most important email and files separately.
9. If any valid message headers of a virus-email indicate what server the message was sent from, contact the service in question and file a formal complaint.
Don’ts
1. Do not open an email attachment unless you were expecting it and know whom it’s from.
2. Do not open any unsolicited executable files, documents, spreadsheets, etc.
3. Avoid downloading executable or documents from the internet, as these are often used to spread viruses.
4. Never open files with a double file extension, e.g. filename.txt.vbs. This is a typical sign of a virus program.
5. Do not send or forward any files that you haven’t virus-checked first.
6. Viruses and spam
7. Virus-makers and spammers often cooperate in devious schemes to send as much spam as possible as efficiently as possible. They create viruses that infect vulnerable computers around the world and turn them into spam-generating “robots”. The infected computers then send massive amounts of spam, unbeknownst to the computer owner.
Such virus-generated email is often forged to appear to be sent from legitimate addresses collected from address books on infected computers. The viruses also use such data, combined with lists of common (user) names, to send spam to huge numbers of recipients. Many of those messages will be returned as undeliverable, and arrive in innocent and unknowing email users’ Inboxes. If this happens to you, use the trainable spam filter to catch those messages.
How To Get Rid Of Computer Virus
Never the neglect to take action on a computer virus residing in your system. There are chances that you might end up losing important files, programs, and folders. In some cases, the virus damages the system hardware too. Thereby, it becomes mandatory to have an effective anti-virus software installed on your computer to steer clear of all such threats.
Signs of Virus Infection
It is vital for any computer user to be aware of these warning signs –
• Slower system performance
• Pop-ups bombarding the screen
• Programs running on their own
• Files multiplying/duplicating on their own
• New files or programs in the computer
• Files, folders or programs getting deleted or corrupted
• The sound of a hard drive
If you come across any of these above-mentioned signs then there are chances that your computer is infected by a virus or malware. Not to delay, immediately stop all the commands and download an antivirus software. If you are unsure what to do, get the assistance of an authorized computer personnel. If you are confident enough, start investigating on your own by following the below mentioned step-by-step procedures.
#Safe Mode
Boot the system and press F8 for Advanced Boot Options menu. Select Safe Mode with Networking and press Enter. You might need to keep repeatedly pressing to get on to the screen.
Working on the Safe Mode helps handle nefarious files as they’re not actually running or active. Last but not the least the internet spreads the infection, so remove the connection.
#Delete Temporary Files
In order to free the disk space, delete temporary files before starting to run the virus scan. This approach helps speed up the virus scanning process. The Disk Cleanup tool helps in deleting your temporary files on the computer.
Here is how you got to go about accomplishing it – Start menu then select All Programs, now you click on Accessories, System Tools, and then click Disk Cleanup.
#Download Virus/Malware Scanner
If you are under the impression that a virus scanner cleanups the bad stuff from your computer then sadly, that’s not true! It helps in eliminating standard infections and not sufficient to remove the latest harmful infections. The virus/malware scanner helps to narrow down on the issue, so, download it now. In order to better protect go for a real-time anti-virus program, since it automatically keeps checking in the background for viruses.
P.S: Don’t install more than one real-time anti-virus program. If you do so, your system will start to behave weirdly.
#Run a Virus/Malware Scan
Download the virus/malware scanner using the internet. Once you have finished downloading the virus scanner, disconnect it for security and safety reasons. After successful download complete the installation procedures of the Virus/Malware scanner, then start running your on-demand scanner first and thereafter run your real-time scanner.
The reason for running both is that one of them will effectively eliminate your computer virus or malware.
#Reinstall the Software or Damaged Files
Once the virus removal from your computer is complete, go ahead and reinstall the files and programs that were damaged by the virus or malware. Make use of the backups for re-installation.
In simple, do the backups regularly and stay protected.
Coronavirus Malware
Protect your computer from every type of virus with Comodo Free Antivirus.
Related Resources:
Antivirus for Mac
Wikipedia DDOS Attack
Best Virus Removal
Antivirus Software
Antivirus App for Android
Antivirus for Windows 7
Virus Removal
Antivirus for PC
Website Virus Scan
Website Safety Check
Cheapest CDN
Remote Desktop Connection Manager
What is Internet Security?
iloveyou virus
Best Website Security
Website Checker
Website Vulnerability Scanner
Website Malware Scanner
Website Status
Free Website Hosting
Website Backup
Password Hacker
Web Application Protection
Web Security Check
Website Protection Software
Best DDoS Protection
Best Remote Desktop Software
How to Secure your Website
Check Website Safety
What does HTTPS Mean
Website Malware Removal
Website Scanner
Link Scanner
Check Website Reputation
What is Hashing
Check Website for Malware
Website Scam Checker
Is This Website Safe
How to Learn Hacking
Managed Detection and Response
FAQ Pages
A computer virus is a malicious program that self-recreates by replicating itself to another program. As it were, the computer virus spreads independently from anyone else into other executable code. The reason for making a computer virus is to infect vulnerable systems, gain administrator control and take user delicate information.
Load More
Posted by seo on January 27, 2020
Most Antivirus software battles threats they know, not new ones they’ve never encountered. This strategy leaves open a window of vulnerability from unknown threats that can last for hours or even days. Eg. Comodo Windows Antivirus has a better approach. It’s based on the concept of prevention, not detection.
Load More
Posted by seo on January 27, 2020
1. Boot Sector Virus
2. Direct Action Virus
3. Resident Virus
4. Multipartite Virus
5. Polymorphic Virus
6. Overwrite Virus
7. Spacefiller Virus
Load More
A computer virus is a sort of malware that attaches itself to another program and can replicate and propagate once it has been installed on a user’s computer. When a computer changes the way in which it should work normally, it is said to be infected by a virus. This virus may spread from one computer to another. For example, you may receive an email with a harmful attachment, inadvertently open the file, and the computer virus then infects your machine. Or in other words, a harmful software application that is installed without the user’s knowledge/ consent on their computer and then performs some malicious acts is known as a virus. A virus attaches itself to another software, once infected the system, in such a way that the host program’s execution activates the virus’s actions simultaneously. It has the ability to self-replicate itself into other programs or files and infecting them. Computer viruses are harmful but the majority of them engage in malicious activity, such as data destruction.
History of Computer Virus:
Viruses have been infecting various devices for a long term via the Internet or some other medium. The viruses are created with an intention to steal information, completely destroy the device, etc. The “Creeper system, ” the first computer virus, was an experimental self-Multiplying virus launched in 1971. Then, the Rabbit virus came in the mid-1970s and was extremely active and it self-replicated very fast & wrecked the functionality at the same speed. The first PC virus was known as “Elk Cloner” and was built in 1982, by Rich Skrenta. It spread by a floppy disc with a game on it and hooked itself to the Apple II operating system.
“Brain,” the first computer virus for MS-DOS, was introduced in 1986. The boot sector of the floppy disc would be overwritten, preventing the computer from booting. It was created by two Pakistani brothers and was intended to be used as a copy protection system. In 1988, the age of catastrophic viruses began. Most viruses were basically joked with humorous names and messages till then. In 1988, “The Morris” was the first virus that propagated widely.
Types of computer virus
- Boot sector virus: This virus infects the boot sector of the computer and runs every time the computer boots and before the operating system loads. Floppy discs and other bootable media become infected. They are sometimes referred to as memory viruses because they do not infect the file system.
- File Virus: Infects the system by appending itself to the end of a file. It changes the start of a program such that the control jumps to its code.
- Email-Virus: They are comprised of malicious code that is propagated through email messages and can be activated when a user clicks on a link in an email message, opens an email attachment, or interacts in any manner with the infected email message.
- Polymorphic Virus: Poly means many and morphic means forms. So this virus changes its form every time. A virus signature is a pattern that can be used to assess whether a virus exists or not (a series of bytes that make up virus code). This virus changes itself every time when it is installed so that it can avoid detection by antivirus software. Here, only the signature of this virus is updated, the functionality remains the same.
- Macro Virus: These viruses are activated when a program capable of performing a macro is executed. Macro viruses, for example, can be found in spreadsheet files.
- Multipartite Virus: This virus has the power to infect a computer’s boot sector, memory, and files, among other areas. This complicates its detection and containment.
- Encrypted Virus: To avoid detection by antivirus software, this type of virus is encrypted. There’s also a decryption algorithm included. As a result, before running, the virus decrypts.
- Stealth Virus: This virus is difficult to detect because it modifies the code used to detect it. As a result, virus detection is extremely difficult.
- Resident Virus: A virus that saves itself in the computer’s memory before infecting additional files and programs after the original software stops working. Because it is hidden in the computer memory and difficult to remove, this virus can easily infect other files.
- Direct action Virus: If a virus is tied to an executable file and when the file is opened or run, that virus gets installed/ spread, it is known as “direct action”. This virus does not delete any files or lay impact on the speed of the system; it just renders your files inaccessible.
- Browser Hijacker Virus: This virus attacks and can adjust the computer browser’s settings. it can also force your browser to malicious sites.
What does a computer virus do?
A virus can harm or destroy data, slow down system resources, and log keystrokes, among other things. A virus has the ability to have unexpected or harmful outcomes during this procedure, such as destroying system software by corrupting data. Some computer viruses are designed to damage your computer by destroying files, corrupting applications, or reformatting the hard drive. Even less dangerous computer infections can have a substantial impact on your system’s performance, eating up RAM and triggering frequent crashes. Other viruses may just clone themselves or flood a network with traffic, rendering all internet activity difficult.
How a computer gets a virus?
Through the following activities you may get your device infected by the virus :
- Sharing the data like music, files, and images with each other.
- If you open a spam email or an attachment in an email that is sent by an unknown person.
- Downloading the free games, toolbars, media players, etc.
- Visiting a malicious website.
- Installing pirated software(s) etc.
Symptoms of a computer virus?
If your system is infected by the virus, the following symptoms may be seen :
- Opening of Pop-up window frequently: Pop-ups may entice you to visit odd locations. They will take you to a page to download any antivirus (which is actually not an antivirus), or other harmful software.
- Slowing down of system without any reason.
- Updated homepage: For example, the homepage is replaced by a website and you would not be able to undo that replacement.
- Identifying that your files are corrupted.
- Change in the name of your hard drive & also change in its volume.
- Change in amount of free memory available.
- Not able to find your files or programs.
- Unknown change in the password that does not let you login.
- A virus may damage your hard drive and our device may freeze or crash as a result of this.
How to remove computer viruses?
To get rid of a computer infection, you have two options:
- Do-it-yourself manual approach
- Seek the assistance of a reliable antivirus product.
In the manual approach, online search is usually the first step in this approach. You can be requested to complete a huge list of tasks. To finish the procedure, you’ll need time and maybe some experience.
The simpler approach is to install antivirus. Antivirus software is a program that searches for, detects, prevents, and removes software infections that can harm your computer. Antivirus can also detect and remove other dangerous software such as worms, adware, and other dangers. This software is intended to be used as a preventative measure against cyber dangers, keeping them from entering your computer and causing problems. Antivirus is available for free as well. Anti-virus software that is available for free only provides limited virus protection, whereas premium anti-virus software offers more effective security. For example Avast, Kaspersky, etc.
Sample Question
Question 1. How can you protect your computer system from viruses?
Solution:
We can use antivirus software to keep your computer safe from viruses. Antivirus software works by comparing the files and programs on your computer to a database of known malware types. It will also monitor computers for the presence of new or undiscovered malware threats, as hackers are constantly generating and propagating new viruses.
Question 2. Make a list of frequent computer virus infection sources.
Solution:
The sources via which you can infect your system with viruses are :
1. Downloading programs/software from the internet.
2. Emails
3. External devices like pen-drives
4. Using an unknown CD to Boot data
5. Bluetooth/ infrared
Question 3. Why is it a good idea to back up data on a regular basis?
Solution:
Files that have been damaged can be restored by backup.
Question 4. How do computer viruses spread?
Solution:
Computer viruses are typically propagated by email, file sharing, or CDs or by downloading file(s) from unauthenticated sources.
Question 5. What is a computer virus?
Solution:
It is a harmful software application that is installed without the user’s knowledge/ consent on their computer and then performs some malicious acts, is known as a virus. It attaches itself to another software, once infected the system, in such a way that the host program’s execution activates the virus’s actions simultaneously.